UVK Help - Home section


When you open UVK, the Home page is displayed, like the picture below.
Note that you can launch UVK by pressing the following set of keys: Ctrl + Alt + U.
Content index:
Customizable buttons (custom apps)
Screenshot

Oveview of the Home page
The UVK's Home page, also known as Main menu is the user interface normally displayed when you launch the application. It consists of a window containing 30 buttons.
Click a button to run the indicated module. In order to know what each module does see Features of each module below.
Most of the modules will show a Home button, that you can click to return to the starting point. This simple back and forth procedure allows you to navigate through most of the UVK's features without the need of a permanent side/top bar having all the buttons, which would constantly use a large ammount of precious space in the GUI.
The disposition of the buttons is organized in three sections:
The six small buttons at the top will jump to
application related features.
The six buttons in the left bottom
area of the window refer to system repair and optimization features.
The sixteen buttons in the right side refer to miscellaneous features,
such as tweaking, backup, recovery, system information and others.
Below is the list of actions you can perform after clicking the corresponding button in the welcome screen.
Customizable buttons (custom apps)
Starting with version 11.9, UVK offers you 19 buttons that can download one or two files and execute up to four commands. Clicking the last button in the right pane (More custom apps) brings up a dialog box with 18 customizable buttons,similar to the picture below.
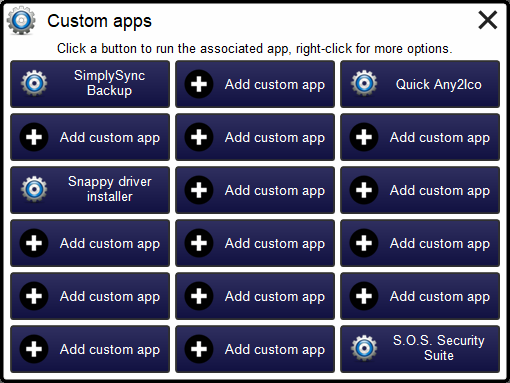
By default, the buttons are named Add custom app, and they behave as Custom third party apps, in the System repair module. Each app can download one or two files from the Internet, and run up to four commands. Also each command can be a single line UVK scripting command, but multiple line commands will not work.
Clicking an empty button opens a dialog box where you can configure your custom app for the selected button. Please see Custom third party apps for instructions. Once you setup your custom buttons, just right-click over them to get additional options: Edit extra app, and Delete extra app.
Custom apps can be exported to UVKSettings.ini, and syncronized through CloudSync. So, if you own a valid UVK license, you can automatically load your custom apps in every computer you run UVK.
Features of each module
System booster
![]() Improve system performance and reduce registry size by removing
invalid registry keys and values.
Improve system performance and reduce registry size by removing
invalid registry keys and values.![]() Improve the Windows shell's responsiveness by removing invalid
shortcuts.
Improve the Windows shell's responsiveness by removing invalid
shortcuts.![]() Free up hard disk space by removing unnecessary (junk) files and old
restore points.
Free up hard disk space by removing unnecessary (junk) files and old
restore points.![]() Export the list of items found to a text file.
Export the list of items found to a text file.
![]() Defragment
the Windows registry.
Defragment
the Windows registry.
![]() Create
system restore points and register the system files.
Create
system restore points and register the system files.
![]() Cleanup all
temporary files and browsers cache.
Cleanup all
temporary files and browsers cache.
![]() Backup and
restore the Windows registry.
Backup and
restore the Windows registry.
Smart uninstaller
![]() Uninstall several programs at once, and in automated mode, if
desired.
Uninstall several programs at once, and in automated mode, if
desired.![]() Force uninstall of stubborn programs.
Force uninstall of stubborn programs.![]() Add custom uninstall entries to the uninstall list.
Add custom uninstall entries to the uninstall list.![]() Get information about the uninstall entry.
Get information about the uninstall entry.![]() Delete the uninstall entry without uninstalling the program.
Delete the uninstall entry without uninstalling the program.![]() Change the uninstall entry's icon.
Change the uninstall entry's icon.![]() Verify the uninstall file's signature.
Verify the uninstall file's signature.![]() Get the uninstall file's VirusTotal report.
Get the uninstall file's VirusTotal report.![]() Open the file system location of the program's folder or the
uninstaller file.
Open the file system location of the program's folder or the
uninstaller file.![]() Open the uninstall entry's help/info url.
Open the uninstall entry's help/info url.![]() Hide Microsoft signed files from the list.
Hide Microsoft signed files from the list.![]() Change the way the uninstall entries are dysplayed in the list.
Change the way the uninstall entries are dysplayed in the list.![]() And much more...
And much more...
Quick user manager
![]() Manage all
user accounts in your system, including buil-in accounts.
Manage all
user accounts in your system, including buil-in accounts.
![]() Easily add
new user accounts, and simmultaneously set their password, privilege
level and associated picture.
Easily add
new user accounts, and simmultaneously set their password, privilege
level and associated picture.
![]() Remove user
accounts in two clicks.
Remove user
accounts in two clicks.
![]() Change or
remove the password for any user account.
Change or
remove the password for any user account.
![]() Change the
picture associated with any user account.
Change the
picture associated with any user account.
![]() Auto-logon
a user account.
Auto-logon
a user account.
![]() Hide a user
account from the welcome screen.
Hide a user
account from the welcome screen.
![]() Enable,
disable user accounts and much more.
Enable,
disable user accounts and much more.
System immunization
![]() Prevent the
most vulnerable registry and file system areas from being infected.
Prevent the
most vulnerable registry and file system areas from being infected.
![]() Prevent adding
programs to the windows startup and logon.
Prevent adding
programs to the windows startup and logon.
![]() Prevent
creating/deleting browser helper objects, Internet explorer toolbars
and search providers.
Prevent
creating/deleting browser helper objects, Internet explorer toolbars
and search providers.
![]() Prevent
modifying the internet settings and the Internet explorer startup
pages.
Prevent
modifying the internet settings and the Internet explorer startup
pages.
![]() Prevent
executing files in specific directories.
Prevent
executing files in specific directories.
![]() Backup and
restore the Windows registry.
Backup and
restore the Windows registry.
System repair
![]() Repair your
computer with more than fifty exclusive fixes: Register system dlls,
enable and repair Windows update, clear dns cache and the hosts
file, reset user default registry settings, fix installation
problems, empty all browsers cache, reset security settings,
defragment and optimize the hard drives, install Java, Flash,
DirectX, .Net Framework, Fix the WMI and the system restore, delete
all restore points, fix the windows shell, reset the user shell
folders and much more.
Repair your
computer with more than fifty exclusive fixes: Register system dlls,
enable and repair Windows update, clear dns cache and the hosts
file, reset user default registry settings, fix installation
problems, empty all browsers cache, reset security settings,
defragment and optimize the hard drives, install Java, Flash,
DirectX, .Net Framework, Fix the WMI and the system restore, delete
all restore points, fix the windows shell, reset the user shell
folders and much more.
![]() Automate
the most popular malware removal tools: MalwareBytes AntiMalware,
Super AntiSpyware, Rogue Killer, Kaspersky TDSSKiller, Avast! aswMBR,
AdwCleaner, Junkware Removal Tool and Avast! Browser Cleanup .
Automate
the most popular malware removal tools: MalwareBytes AntiMalware,
Super AntiSpyware, Rogue Killer, Kaspersky TDSSKiller, Avast! aswMBR,
AdwCleaner, Junkware Removal Tool and Avast! Browser Cleanup .
![]() Create your
own apps, which can automatically download and run files.
Create your
own apps, which can automatically download and run files.
![]() Create
professional html reports of all the actions performed in this
section.
Create
professional html reports of all the actions performed in this
section.
![]() Import/Export everything to a file, allowing you to run the desired
fixes and apps with a couple of clicks.
Import/Export everything to a file, allowing you to run the desired
fixes and apps with a couple of clicks.
Threat Scanner
![]() Detect and
remove adware for all the users in your system in less than two
minutes.
Detect and
remove adware for all the users in your system in less than two
minutes.
![]() Detect and
remove browser toolbars, ad-ons, plugins, unwanted search providers
and hijacked home pages, and also potentially unwanted programs
(PUP's).
Detect and
remove browser toolbars, ad-ons, plugins, unwanted search providers
and hijacked home pages, and also potentially unwanted programs
(PUP's).
![]() Detect and
remove Internet browser hijackers, such as malicious extensions and
ad-ons, hijacked shortcuts and infected startup pages and search
engins. Support for nearly all browsers has been recently added.
Detect and
remove Internet browser hijackers, such as malicious extensions and
ad-ons, hijacked shortcuts and infected startup pages and search
engins. Support for nearly all browsers has been recently added.
DiskCopy
![]() Copy an MBR disk to a GPT one and the inverse.
Copy an MBR disk to a GPT one and the inverse.![]() Select the partitions to copy.
Select the partitions to copy.![]() Copy a single partition and make the target disk bootable.
Copy a single partition and make the target disk bootable.![]() Erase and initialize a disk.
Erase and initialize a disk.![]() Convert a MBR disk to GPT and the inverse.
Convert a MBR disk to GPT and the inverse.![]() Make a disk offline or read-only.
Make a disk offline or read-only.![]() View disk detailed information.
View disk detailed information.![]() Delete partitions.
Delete partitions.![]() Create partitions
Create partitions![]() Format partitions.
Format partitions.![]() Set the volume label, the drive letter and the access paths
Set the volume label, the drive letter and the access paths![]() Set partition/volume advanced options.
Set partition/volume advanced options.![]() Scan and repair volumes.
Scan and repair volumes.![]() Optimize volumes.
Optimize volumes.![]() Make partitions bootable.
Make partitions bootable.![]() View partition and volume detailed information.
View partition and volume detailed information.
Clear Disk Info
![]() Get
a clear view of health related information about connected storage
devices.
Get
a clear view of health related information about connected storage
devices.
![]() Export
the disk's S.M.A.R.T./NVMe information to a text file.
Export
the disk's S.M.A.R.T./NVMe information to a text file.
![]() Monitor the disks and get warnings when their health status changes.
Monitor the disks and get warnings when their health status changes.
![]() Check
disks for errors and repair them.
Check
disks for errors and repair them.
![]() Optimize the disks.
Optimize the disks.
![]() Eject
the disks.
Eject
the disks.
Process manager
![]() Filter all the running processes by their executable path.
Filter all the running processes by their executable path.
![]() Select and manage several processes at once.
Select and manage several processes at once.
![]() Kill processes.
Kill processes.
![]() Kill several processes with the same path at once.
Kill several processes with the same path at once.
![]() Kill processes and delete the parent files simultaneously.
Kill processes and delete the parent files simultaneously.
![]() Kill several processes using special filters.
Kill several processes using special filters.
![]() Delete the
whole parent directory of a process.
Delete the
whole parent directory of a process.
![]() Pause and resume processes.
Pause and resume processes.
![]() Verify the processes files signatures.
Verify the processes files signatures.
![]() Search information about a process over the internet.
Search information about a process over the internet.
![]() Get the
VirusTotal report of the running files.
Get the
VirusTotal report of the running files.
![]() Open the
running files location.
Open the
running files location.
![]() View the
running files properties.
View the
running files properties.
![]() Manage the
services running in a specific process.
Manage the
services running in a specific process.
Memory modules manager
![]() List all
loaded memory modules.
List all
loaded memory modules.
![]() Search
information about the memory modules over the internet.
Search
information about the memory modules over the internet.
![]() Verify the
memory modules files signatures.
Verify the
memory modules files signatures.
![]() Filter the
modules list. You can hide system protected files, all Microsoft
files, or all digitally signed files.
Filter the
modules list. You can hide system protected files, all Microsoft
files, or all digitally signed files.
![]() Get the VirusTotal report
of the memory modules.
Get the VirusTotal report
of the memory modules.
![]() Open the
memory modules file locations.
Open the
memory modules file locations.
![]() View the
memory modules file properties.
View the
memory modules file properties.
![]() Delete
infected memory objects using two diferent methods.
Delete
infected memory objects using two diferent methods.
Autorun manager
![]() Delete
autorun
entries, scheduled tasks and the corresponding files simultaneously.
Delete
autorun
entries, scheduled tasks and the corresponding files simultaneously.
![]() Select and
manage several autorun entries at once.
Select and
manage several autorun entries at once.
![]() Verify the
autorun entries file signatures.
Verify the
autorun entries file signatures.
![]() Filter the
autoruns list. You can hide system protected files, all Microsoft
files, or all digitally signed files.
Filter the
autoruns list. You can hide system protected files, all Microsoft
files, or all digitally signed files.
![]() Search
information about a autorun entry file over the internet.
Search
information about a autorun entry file over the internet.
![]() Get the VirusTotal report
of the autorun files.
Get the VirusTotal report
of the autorun files.
![]() Jump to the
registry key where the autorun entry is located.
Jump to the
registry key where the autorun entry is located.
![]() Open the
autorun entries file locations.
Open the
autorun entries file locations.
![]() View the
autorun entries file properties.
View the
autorun entries file properties.
![]() Maximizable
window in this section for a more comfortable view.
Maximizable
window in this section for a more comfortable view.
Service manager
![]() Delete
services or drivers, and the corresponding files simultaneously.
Delete
services or drivers, and the corresponding files simultaneously.
![]() Perform all
common service management tasks: Stop, start, pause, resume
services, and set their startup type.
Perform all
common service management tasks: Stop, start, pause, resume
services, and set their startup type.
![]() Select and
manage several services or drivers at once.
Select and
manage several services or drivers at once.
![]() Stop all non
Microsoft services.
Stop all non
Microsoft services.
![]() Filter the
services list. You can hide system protected files, all Microsoft
files, or all digitally signed files.
Filter the
services list. You can hide system protected files, all Microsoft
files, or all digitally signed files.
![]() Verify the
services/drivers file signatures.
Verify the
services/drivers file signatures.
![]() Search
information about a service/driver file over the internet.
Search
information about a service/driver file over the internet.
![]() Get the VirusTotal report
of the service/driver file.
Get the VirusTotal report
of the service/driver file.
![]() Jump to the
registry key where the service/driver is located.
Jump to the
registry key where the service/driver is located.
![]() Open the
service/driver file location.
Open the
service/driver file location.
![]() View the
service file properties.
View the
service file properties.
![]() Jump to the
service's process in the Process manager.
Jump to the
service's process in the Process manager.
![]() Maximizable
window in this section for a more comfortable view.
Maximizable
window in this section for a more comfortable view.
Alternate streams manager
![]() Recursively
scan a drive or folder for alternate data streams.
Recursively
scan a drive or folder for alternate data streams.
![]() Search
information about the streams over the internet.
Search
information about the streams over the internet.
![]() Verify the ADS
files signatures.
Verify the ADS
files signatures.
![]() Read the
streams contents.
Read the
streams contents.
![]() Get the MD5 VirusTotal report
of the streams.
Get the MD5 VirusTotal report
of the streams.
![]() Open the
streams file locations.
Open the
streams file locations.
![]() Delete one,
several or all the streams found.
Delete one,
several or all the streams found.
Delete or replace file or folder
![]() Delete files
and folders even if they're being used by applications.
Delete files
and folders even if they're being used by applications.
![]() Delete running
executable files.
Delete running
executable files.
![]() Delete files
and folders you can't normally delete from the Windows explorer.
Delete files
and folders you can't normally delete from the Windows explorer.
![]() Delete the files
permanently or move them to the recycle bin.
Delete the files
permanently or move them to the recycle bin.
![]() Replace or
copy files.
Replace or
copy files.
![]() Expand
compressed files.
Expand
compressed files.
![]() Replace files
even if they are loaded in the memory.
Replace files
even if they are loaded in the memory.
Scan and create log
![]() Perform a full
analysis of your system and save it to a text file that you can send
to a friend or professional, post in a forum, or analyze it
yourself.
Perform a full
analysis of your system and save it to a text file that you can send
to a friend or professional, post in a forum, or analyze it
yourself.
![]() Choose the
areas you want to scan and show in the log.
Choose the
areas you want to scan and show in the log.
![]() Choose whether
to show Microsoft signed files in the log.
Choose whether
to show Microsoft signed files in the log.
![]() Choose where
to save the log.
Choose where
to save the log.
![]() Choose whether
to verify the scanned files digital signatures.
Choose whether
to verify the scanned files digital signatures.
![]() Search for
recently created files, and write them to the log.
Search for
recently created files, and write them to the log.
![]() Perform other
custom scans, such as retrieving specific information on files,
folders, registry entries, or automatically get the VirusTotal
analysis result for a file.
Perform other
custom scans, such as retrieving specific information on files,
folders, registry entries, or automatically get the VirusTotal
analysis result for a file.
Run Scripts
![]() Disinfect your
computer by pasting lines from the UVK log to delete corresponding
registry entries and files.
Disinfect your
computer by pasting lines from the UVK log to delete corresponding
registry entries and files.
![]() Use custom
commands to download files, execute programs, delete or add registry
entries, terminate processes, delete files and folders, run cmd
batch scripts, register system files, run the
UVK Fixes and much more.
Use custom
commands to download files, execute programs, delete or add registry
entries, terminate processes, delete files and folders, run cmd
batch scripts, register system files, run the
UVK Fixes and much more.
![]() Create system
restore points, empty the recycle bin and all users temporary
folders.
Create system
restore points, empty the recycle bin and all users temporary
folders.
![]() Create and run
scripts that perform complete system repair, maintenance and
optimization.
Create and run
scripts that perform complete system repair, maintenance and
optimization.
![]() Automatically
run any of the UVK fixes or scans.
Automatically
run any of the UVK fixes or scans.
Tools and tweaks
![]() Run useful
Windows or third party tools such as the registry editor, msconfig,
the decice manager, the windows console, the task manager, Blue
screen viewer, Windows installer cleanup tool, .NET framework
cleanup tool and much more, all in one click.
Run useful
Windows or third party tools such as the registry editor, msconfig,
the decice manager, the windows console, the task manager, Blue
screen viewer, Windows installer cleanup tool, .NET framework
cleanup tool and much more, all in one click.
![]() Quickly
enable/disable Windows features such as the administrator account,
the user account control, the system restore, the hibernation, view hidden files and much more.
Quickly
enable/disable Windows features such as the administrator account,
the user account control, the system restore, the hibernation, view hidden files and much more.
![]() Repair the
file associations that are most commonly corrupted by malware: exe,
com, msi, bat, cmd, reg and vbs.
Repair the
file associations that are most commonly corrupted by malware: exe,
com, msi, bat, cmd, reg and vbs.
![]() Prevent
those file associations from being infected/corrupted.
Prevent
those file associations from being infected/corrupted.
![]() Backup user
profiles.
Backup user
profiles.
![]() Unlock
locked folders.
Unlock
locked folders.
![]() Open a file
or internet location.
Open a file
or internet location.
![]() Retrieve al
sorts of information on any file.
Retrieve al
sorts of information on any file.
![]() Generate
VirusTotal reports, deny or grant access, or perform an sfc
scan for any file.
Generate
VirusTotal reports, deny or grant access, or perform an sfc
scan for any file.
![]() Search
information on files and registry entries over the internet.
Search
information on files and registry entries over the internet.
![]() Grant access
or prevent changes to registry keys.
Grant access
or prevent changes to registry keys.
![]() Enumerate all
the restore points.
Enumerate all
the restore points.
![]() Select and
delete one or several restore points.
Select and
delete one or several restore points.
![]() Create system
restore points.
Create system
restore points.
![]() Enable or
disable the system restore.
Enable or
disable the system restore.
System Info
![]() Show
information that can be very useful specially if you're going to
reinstall windows or if you need to diagnose a performance or
hardware problem. This includes the processor, memory and page file
usage, OS and office product keys, and hardware, software and user
accounts info.
Show
information that can be very useful specially if you're going to
reinstall windows or if you need to diagnose a performance or
hardware problem. This includes the processor, memory and page file
usage, OS and office product keys, and hardware, software and user
accounts info.
![]() Export this
info to a comprehensive html file.
Export this
info to a comprehensive html file.
Registry seeker
![]() Scan the
registry for several text strings simultaneously.
Scan the
registry for several text strings simultaneously.
![]() Display the
matched keys and values for eact string in a separate group.
Display the
matched keys and values for eact string in a separate group.
![]() Securely
remove the selected keys/values by performing a backup before
removal.
Securely
remove the selected keys/values by performing a backup before
removal.
![]() Forced
removal of the selected keys/values.
Forced
removal of the selected keys/values.
WAU Manager
![]() Update device drivers through Windows Update.
Update device drivers through Windows Update.
![]() Search
for driver updates, Software updates or both.
Search
for driver updates, Software updates or both.
![]() Update
Windows.
Update
Windows.
![]() Disable/Enable the built in Windows automatic updates.
Disable/Enable the built in Windows automatic updates.
![]() Schedule the application to automatically update Windows at a
specific date and time.
Schedule the application to automatically update Windows at a
specific date and time.
![]() Update
Windows regularly based with the built in scedule.
Update
Windows regularly based with the built in scedule.
![]() Uninstall installed Windows updates.
Uninstall installed Windows updates.
![]() Prevent Windows updates from being installed.
Prevent Windows updates from being installed.
![]() Update
Windows defender definitions even when the Windows automatic updates
are disabled.
Update
Windows defender definitions even when the Windows automatic updates
are disabled.
![]() Fully
replace the Windows automatic updates system.
Fully
replace the Windows automatic updates system.
RebootExec Utilities
![]() Configure or launch the Desktop
Watermark.
Configure or launch the Desktop
Watermark.
![]() Launch
Stop Resetting My Apps.
Launch
Stop Resetting My Apps.
![]() Launch
Multiple Reboot Scheduler.
Launch
Multiple Reboot Scheduler.
![]() Launch
Account Profile Fixer.
Launch
Account Profile Fixer.
![]() Enable
or disable the System Immunization
or Execute Prevent.
Enable
or disable the System Immunization
or Execute Prevent.
Options
![]() Password protect running UVK.
Password protect running UVK.
![]() Change the program's preferences.
Change the program's preferences.
![]() Cancel check the system drive or reset the user default settings on reboot.
Cancel check the system drive or reset the user default settings on reboot.
![]() Run the Log analyzer,
check for updates, report a bug or send a comment.
Run the Log analyzer,
check for updates, report a bug or send a comment.
![]() Customize the UVK's interface by choosing one from
11 available skins.
Customize the UVK's interface by choosing one from
11 available skins.
Reporting
![]() Send the
application reports to your email address.
Send the
application reports to your email address.
![]() Send the
application reports to your FTP server.
Send the
application reports to your FTP server.
![]() Choose
which files to embed in the report.
Choose
which files to embed in the report.
Health Check
![]() Take a
quick look at your computer's health status..
Take a
quick look at your computer's health status..
![]() Fix
the issues found or get instructions on how to..
Fix
the issues found or get instructions on how to..
![]() Easily
enable/disable the System Immunization or Exevute Prevent.
Easily
enable/disable the System Immunization or Exevute Prevent.
![]() Know
the date and time of the last Threat Scan.
Know
the date and time of the last Threat Scan.
![]() Start
a new Threat scan in onel click
Start
a new Threat scan in onel click
Clicking the Help button or pressing F1 will bring you to this page.
Clicking the About button will display a dialog box showing information about the current UVK version and the product activation, as well as options to purchase and install a UVK license.
