UVK Help - VirusTotal Analysis


Overview of the "VirusTotal Analysis" feature
UVK has supported VirusTotal analysis of files and URLs since several years ago, but this feature has been largely improved in the version 7.6.
The Process Manager, Autorun Manager, Service Manager and Smart Unistaller lists have a new column, named VirusTotal, which shows the corresponding item's VirusTotal result directly in the list.
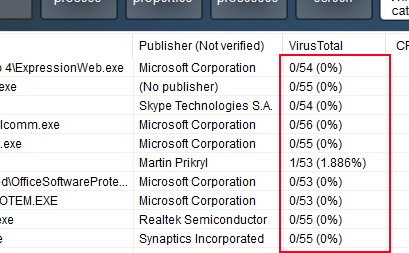
The Memory Modules Manager also supports VT analysis, but it works a bit differently. Because the list of modules is shown as a columnless tree, the VirusTotal result is appended to the module's file path, and separated from it by " | " (a vertical bar with a white space in each side).
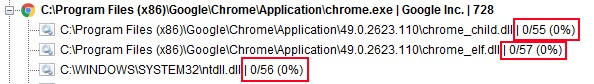
In any case, the result will include the number of positive detections, the number of AV engines, and the detection rate percent.
By default, UVK will automatically start filling out the VirusTotal field of the lists, unless you have disabled that feature in the Options section.
In addition to showing the VirusTotal result of each item, you can also request UVK to hide all items with clean VirusTotal results. This will make it much easier to find and remove malware directly from the lists.
UVK is also able to generate detailed HTML reports of VirusTotal analysis. Also, they can contain the results of the VirusTotal analysis of several files or URLs. Please see Understanding the VirusTotal results below for more information.
The lists VirusTotal related features can be accessed from the list's context menu.
Setting up the VirusTotal options
VirusTotal related settings can be configured in the Options section. Also, as most of the UVK options, they can be exported to an INI file, which is automatically loaded by the UVK setup or portable packages. More info here.
The VirusTotal settings can be found in the Preferences area, as shown in the picture below.
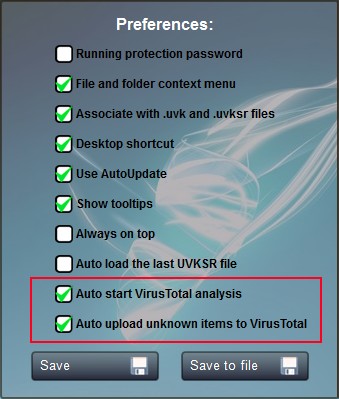
![]() Auto
start VirusTotal analysis: Whether to automatically start
filling out the Virustotal field of the lists. This option is
enabled by default. If you diable this option, you will have to
click the Update VirusTotal results context menu item in
order to update the results. This option is valid for the Process Manager, Autorun Manager,
Service Manager and Smart Unistaller lists.
Auto
start VirusTotal analysis: Whether to automatically start
filling out the Virustotal field of the lists. This option is
enabled by default. If you diable this option, you will have to
click the Update VirusTotal results context menu item in
order to update the results. This option is valid for the Process Manager, Autorun Manager,
Service Manager and Smart Unistaller lists.
![]() Auto
upload unknown items to VirusTotal: This option is enabled by
default. It sets whether UVK should upload files to VirusTotal if
the corresponding report does not exist. We highly recommend you
keep this option enabled.
Auto
upload unknown items to VirusTotal: This option is enabled by
default. It sets whether UVK should upload files to VirusTotal if
the corresponding report does not exist. We highly recommend you
keep this option enabled.
After changing any of the above options, you need to press Save in order for changes to be applied.
VirusTotal context menu
The context menu of the Process Manager, Autorun Manager, Service Manager and Smart Unistaller lists contains a few items that execute ViruStotal related features, as shown in the screenshot below.
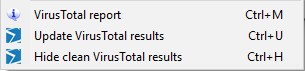
The VirusTotal report menu item creates an HTML report of the selected item(s). The report is automatically opened with 2Browse.
Click the Update VirusTotal results menu item to manually update the list's VirusTotal column.
Click the Hide clean VirusTotal results menu item to make UVK hide items having 0 positive virus detections.
Please see Understanding the VirusTotal results below to ensure a good interpretation of the VirusTotal results.
Understanding the VirusTotal results
VirusTotal results tell you how many antivirus engines have detected a specific file or URL as being malicious. For instance, if a VirusTotal analysis result is 3/53 (5.660%), it means 3 over 53 AV engines have detected the corresponding file or URL as malicious, which makes a detection rate of 5.56%.
While quick VT reports such as the one mentined above can be very useful to quickly identify malware, HTML reports have much more information, such as detection info per AV engine, and it also tells the date at which the AV engine was last updated before this scan. Ensuring the AV engines are up to date helps us to prevent a wrong interpretation of the results. Outdated AV engine results should be ignored. To find out if an AV engine is up to date, compare the date from the AV update column with the one from the Analysis date field of the report item header.
You should not treat a file as malware just because one of the AV engines detected it. Less than 4 detections should be considered a false positive. Please have a look at the the screenshot below. It is the VT HTML report of a genuine Microsoft VC++ runtime installation package, but it still had one detection.
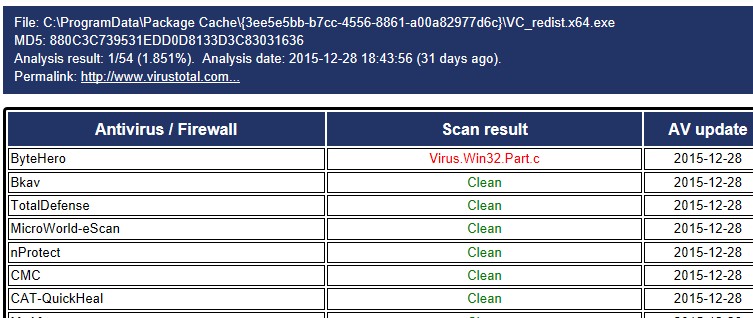
As you can see from the picture above, even though the file being analyzed is a genuine Microsoft installer package, it was detected by ByteHero. This is why you should treat less than four detections as false positives, especially when the AV engines detecting the file are ByteHero, Zillya, Jingamin, Antiy-AVL or TrendMicro. From our experience, those are the engines that gave us the highest number of false positives.
